In 2024, I sat down with Mark Yampolskiy, Associate Professor of Computer Science and Software Engineering at Auburn University, and a recognized expert in cybersecurity issues in additive manufacturing. Our discussion was part of a broader effort to understand the growing cybersecurity risks facing AM workflows, at a time when he was also contributing to ASTM International’s working group on Guidelines for Additive Manufacturing Security.
At the time, the conversation mainly served as an awareness-raising exercise. We explored different scenarios in which AM-specific cybersecurity risks could emerge, often with little visibility around the concrete solutions manufacturers could apply.
Fast forward to today. Government pressure, evolving policy frameworks, and defense procurement practices have fundamentally shifted the conversation. Cybersecurity has moved from a peripheral concern to a selection criterion for suppliers involved in aerospace and defense programs, particularly where digital and additive manufacturing are involved.
This shift refocuses the debate. The question is no longer whether cybersecurity matters, but where exactly it matters in the AM value chain, and which solutions can realistically be implemented in aerospace and defense manufacturing environments.
Among the companies positioning themselves in this space is Materialise. Bart Van der Schueren and Kyle Adriany took 50 minutes of their Wednesday shift to help us make sense of why cybersecurity has become unavoidable for the aerospace and defense industry, and how its digital supply chain security and quality assurance platform sits at the heart of that transformation.
How regulation quietly changed the rules of the game
It is worth emphasizing that cybersecurity, as an eligibility criterion, is no longer optional. In both the United States and Europe, it is now being written into law.
The most recent example is the U.S. National Defense Authorization Act (NDAA), signed into law in December 2025 and previously covered by 3D ADEPT Media. The legislation explicitly introduces requirements related to security, software control, data sovereignty, and qualification for the use of additive manufacturing by the U.S. Department of Defense. It also addresses how AM systems, including their digital and software components, are sourced and approved.
In Europe, a similar shift is underway. The EU’s Cyber Resilience Act (CRA) establishes cybersecurity requirements for products with digital elements, including both hardware and software, and mandates documented security practices as well as incident reporting. Even though these rules are not explicitly framed as “aerospace and defense program requirements”, they effectively raise the baseline level of cybersecurity that European suppliers must meet to remain compliant.
For aerospace primes and defense procurement organizations operating in the EU, or working with European partners, compliance with these regulations therefore becomes a practical prerequisite for supplier consideration.
Beyond a simple compliance checklist, these legislative frameworks push aerospace and defense companies, and their suppliers, to reflect more deeply on what cybersecurity actually means within their business: how it intersects with their manufacturing operations, digital workflows, and the requirements they are expected to meet.
Defining cybersecurity in AM, without the jargon
When you consider that additive manufacturing is still a relatively young and complex technology, one that is constantly reinventing its own rules, you quickly realize that understanding cybersecurity in AM does not require a trip to the Oxford dictionary. It requires looking at how AM is actually used, shared, and scaled in the real world.
As Bart Van der Schueren puts it, “It all comes down to how we define cybersecurity in the context of additive manufacturing. I see two main risks, and they are specific to AM, not manufacturing in general.”
These risks could be summed up as: unauthorized access and unauthorized use. He explains:
- The first risk (unauthorized access) is the most straightforward one. If a company is hacked and critical data is stolen, sensitive aerospace or defense parts could end up in the wrong hands. “That’s something we absolutely want to avoid,” he stresses.
- The second risk (unauthorized use) is closely related, even if it is not always labeled as cybersecurity. Additive manufacturing relies on extremely sensitive materials and digital data, especially in defense and space applications. From an IP owner’s perspective, the issue is not only theft, but misuse. A component may be authorized to be printed once, yet nothing technically prevents it from being printed a hundred times and sold through a parallel channel.
Van der Schueren also points to another, often overlooked dimension of this risk: improper manufacturing. He refers to a case reported in the press in which a small aircraft in the UK crashed during takeoff. Hypothetically, if the air inlet used in that aircraft had been designed to be produced in a heat-resistant material due to its proximity to the engine, printing that same design in PLA would fundamentally compromise its performance. That is essentially what happened: the part softened under heat, collapsed, airflow was interrupted, and the engine failed.
“For an IP owner,” he says, “the goal is to ensure that when digital assets are shared, the part is produced exactly as designed: with the right material, the right machine, and the right orientation. Protecting IP is not just about preventing theft. It is also about ensuring the part performs exactly as intended.”
That said, cybersecurity in additive manufacturing goes well beyond IP protection.
As Kyle Adriany explains, “A huge amount of effort goes into creating IP, from part design to build files and machine parameters. Naturally, you want to protect that IP. You don’t want it leaked, and you certainly don’t want it altered. But beyond ownership, what really matters is that your original intent carries through the entire lifecycle of the part: that it is printed correctly, using the right material, and even maintained in the right way.”
There is also another dimension to consider. Cyberattacks are not always about stealing data.
“In some recent cases, such as the attack involving Jaguar Land Rover, the objective appeared to be production disruption,” Adriany adds. “Taking machines offline, corrupting files, or rendering systems unusable. As additive manufacturing moves from controlled environments into distributed supply chains, this significantly expands the attack surface.”
Cyber risk at the heart of the A&D supply chain
It is no secret that the aerospace and defense (A&D) supply chain is undergoing a profound shift. Long dominated by centralized and tightly controlled production models, it is becoming increasingly decentralized and regionalized, driven by geopolitical tensions, logistical bottlenecks, and the need to manufacture parts closer to where assets are deployed.
While this evolution improves resilience and responsiveness, it also introduces new vulnerabilities. As production moves toward more distributed additive manufacturing models, digital design files, process parameters, and qualification data must circulate across a growing network of suppliers. Each additional node in that network becomes a potential point of failure.
For Kyle Adriany, the nature of the cyberattack matters less than its outcome. “No matter the type of attack,” he explains, “the result is the same: the right part doesn’t arrive where it’s needed.” At that point, cybersecurity stops being a technical issue and becomes a supply chain problem. And in aerospace, disruption rarely stays isolated: a single late or faulty part can ground an entire aircraft.
This is why, Adriany argues, the objective is to ensure that the IP owner’s intent “extends into the supply chain for the entire lifecycle of the part.”
In a distributed manufacturing environment, cybersecurity is not only about protecting data, but about ensuring continuity and trust at every step of the supply chain.
What solution does Materialise bring to the table?
Two years ago, while reflecting on Mark Yampolskiy’s insights, I assumed that the cybersecurity challenges facing additive manufacturing users would eventually open the door to new opportunities. I expected innovative companies with cybersecurity expertise would come from outside the AM industry, to step in and propose solutions tailored to AM users and technology providers.
I found myself looking beyond our industry for solutions that were already taking shape in front of my eyes, gradually reinforced and refined over the years. One of these solutions is Identify3D. Founded in 2014 in San Francisco, the company was acquired by Materialise in 2022 with the goal of turning its CO-AM platform into the most secure platform for distributed manufacturing.
From the outset, Identify3D positioned itself as a digital supply chain security and quality assurance platform, designed to encrypt, distribute, and trace digital part data, preventing counterfeits and ensuring that modified, substandard, or uncertified parts never make it into the physical supply chain.
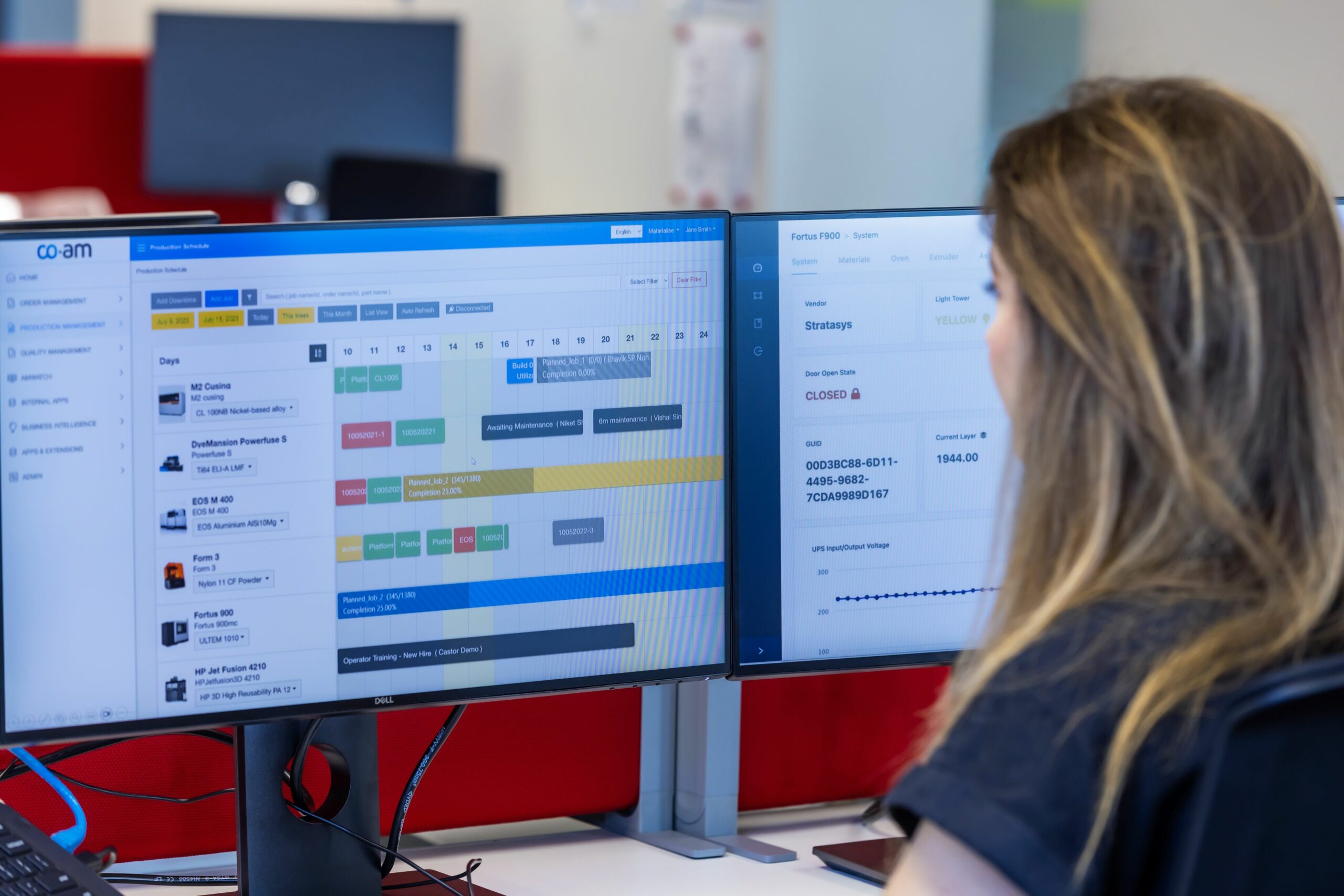
As Kyle Adriany explains, Identify3D enables IP owners to secure their digital assets while retaining control across distributed manufacturing environments. “It allows IP owners to protect their data, control how, where, and how many times a part is produced, and ensure traceability and quality across the supply chain,” he says. “We work closely with machine manufacturers to secure files from the moment they are authored all the way to the machine that prints the part. That’s how we achieve true end-to-end security and traceability.”
Bart Van der Schueren builds on that idea by pointing to what is often the most vulnerable moment in additive manufacturing: the transition from digital to physical. “What’s critical is closing the gap between the digital and the physical,” he explains. “That last mile — going from bits to printed material — is often the weakest link. With deep machine-level integration, even if someone has access to the machine, they cannot misuse the data. This helps eliminate both intentional and unintentional errors.”
How Identify3D helps exactly? By allowing suppliers to isolate qualified workstreams (specific machines, materials, or customers) while maintaining traceability and visibility. In other words, it replaces paperwork-heavy processes with software-driven workflows.
While this solution is particularly relevant to the aerospace and defense industries, it is also applicable across various other sectors.
“Not all parts are critical. Once companies can produce securely, they will naturally attract non-secured work as well. Secure production becomes a multiplier. Defense is leading out of necessity and government pressure, but once distributed spare part production is proven, this approach will expand into aerospace, energy, infrastructure, and beyond,” Materialise CTO confirms.
The beginning of an evolution?
With more than 35 years of experience, Materialise is one of those companies that genuinely embodies the idea that “patience is a virtue”. The team has long understood that meaningful progress takes time, especially in an industry like additive manufacturing, where success depends as much on collaboration and trust as it does on technology.
Rather than chasing quick wins, Materialise has consistently invested in an end-to-end approach, working closely with customers, navigating technical and cultural hurdles, and learning along the way. In a field still defining its own rules, that long-term mindset matters.
As Bart Van der Schueren puts it, the company does not settle for partial answers. The objective is to maintain continuity from IP creation all the way to the printed and qualified part, without breaking the digital or physical chain along the way.
“We’re still at the beginning of an evolution, maybe even a revolution,” he says. “If we get this right, it will unlock enormous opportunities for additive manufacturing and for the entire supply chain. Secured printing can help rebuild trust and bring more production back to service providers.”
After following this industry for years, and watching many promises rise faster than they mature, I am inclined to take their words for it.
Bart Van der Schueren and Kyle Adriany’s statements have been edited for brevity and clarity.
This content has been produced in collaboration with Materialise. All images: Materialise